As the legend of Serial Babacom continues to grow, so do the efforts to unmask this enigmatic figure. Law enforcement agencies, cybersecurity experts, and online sleuths have joined forces to track down Serial Babacom and bring them to justice.
A closer examination of Serial Babacom's activities reveals a pattern of behavior that is both intriguing and disturbing. It appears that Serial Babacom operates with a sense of impunity, often targeting individuals and organizations that have been lax in their cybersecurity measures. serial babacom
Their methods are varied, but often involve a combination of social engineering, phishing attacks, and exploitation of software vulnerabilities. Once they have gained access to a targeted system, Serial Babacom may choose to extract sensitive information, disrupt operations, or simply leave a digital calling card as a signature. As the legend of Serial Babacom continues to
The activities of Serial Babacom have had far-reaching consequences, affecting not only the individuals and organizations directly targeted but also the broader online community. It appears that Serial Babacom operates with a
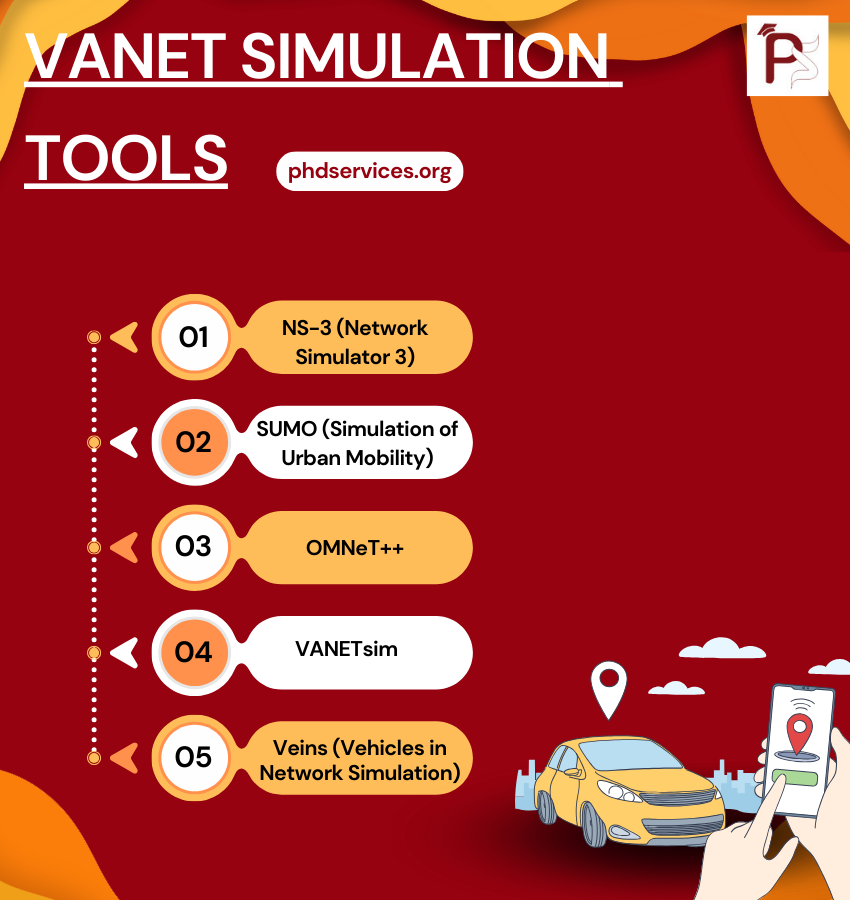
VANET Simulation Tools Topics & Ideas
We utilize cutting-edge VANET Simulation Tools according to your proposed concept. Explore the various Topics & Ideas that are being explored by phdswervices.org. It is common for research students to make mistakes in certain areas, and that is why we offer the guidance of our writers. We ensure that your topic is properly framed with appropriate keywords to enhance its effectiveness.
- Road traffic and geography topology based opportunistic routing for VANETs
- Cooperative pseudonym change scheme based on the number of neighbors in VANETs
- Boosting named data networking for data dissemination in urban VANET scenarios
- VANET Based Vehicle Tracking Module for Safe and Efficient Road Transportation System
- Design and performance evaluation of a PMIPv6 solution for geonetworking-based VANETs
- SEGM: A secure group management framework in integrated VANET-cellular networks
- Secure and privacy-aware traffic information as a service in VANET-based clouds
- A cross layer approach for efficient multimedia data dissemination in VANETs
- Reliability and energy-efficiency analysis of safety message broadcast in VANETs
- Asking neighbors a favor: Cooperative video retrieval using cellular networks in VANETs
- Intelligent Adjustment Forwarding: A compromise between end-to-end and hop-by-hop transmissions in VANET environments
- Performance analysis and implementation of proposed mechanism for detection and prevention of security attacks in routing protocols of vehicular ad-hoc network (VANET)
- A lightweight authentication and privacy-preserving scheme for VANETs using TESLA and Bloom Filters
- LIAP: A local identity-based anonymous message authentication protocol in VANETs
- Practical secure and privacy-preserving scheme for value-added applications in VANETs
- The insights of message delivery delay in VANETs with a bidirectional traffic model
- Nexthop selection mechanism for nodes with heterogeneous transmission range in VANETs
- QualityScan scheme for load balancing efficiency in vehicular ad hoc networks (VANETs)
- A mobility-based scheme for dynamic clustering in vehicular ad-hoc networks (VANETs)
- Regression based critical information aggregation and dissemination in VANETs: A cognitive agent approach